The Anniversary of the Empty Tank: Reflecting on Colonial Pipeline
I was driving through Georgia last week, and I noticed the price on the sign: $4.53 for regular. With crude prices spiking and the usual pre-Memorial Day jitters, it feels like every time we pull up to the pump in 2026, we’re holding our breath. But for those of us who were in the Southeast five years ago this week, that high price brings back a very specific, visceral smell: the scent of panic.
Last week was the anniversary of the Colonial Pipeline hack, and if you think we’ve moved past it, you haven't been paying attention to your network logs (or your gas receipt!).
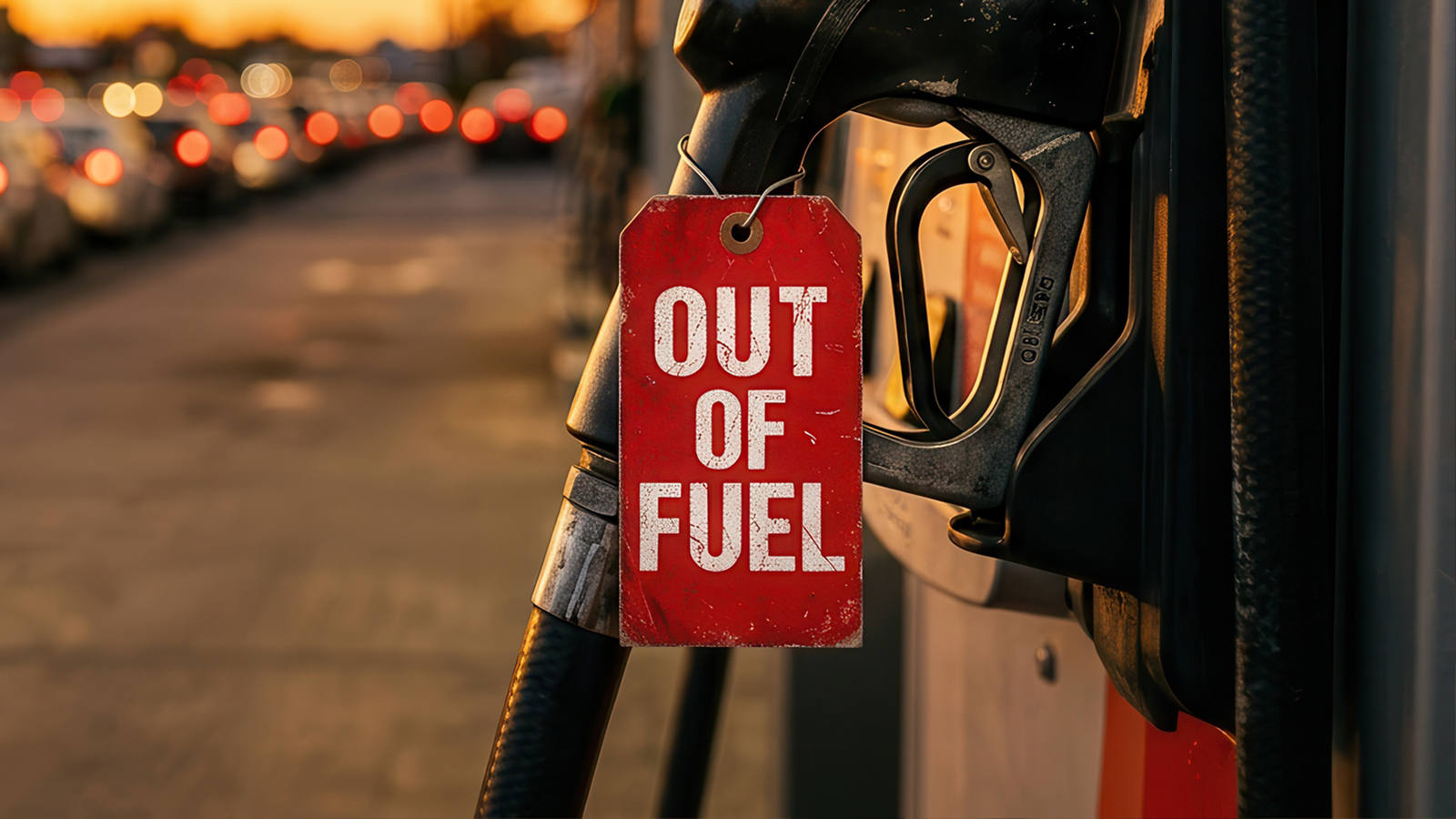
The Great Plastic Bag Panic
Remember May 2021? We saw people filling literal plastic bags with gasoline. It was absurd, but it was driven by a terrifying reality: a single ransomware note had effectively "turned off" the East Coast.
Here is the kicker that still keeps OT engineers up at night: The hackers didn’t even touch the pipeline. The pipeline (pumps, valves, the actual steel in the ground) was perfectly fine. The "hack" was an IT hit on the billing system. Because Colonial couldn’t figure out how to invoice their customers, they decided it was safer to shut down the physical flow of 2.5 million barrels of fuel a day.
This is the ultimate example of Isolation Hubris. We built systems that were "connected for convenience" but "isolated by hope." When the IT side caught a cold, the OT side ended up in the ICU.
IT vs. OT: A Tale of Two Worlds
For years, the industry line has been: "Keep OT separate from IT." We preach air-gaps that aren't actually air-gapped and segmentation that is usually just one misconfigured VLAN away from disaster.
But look at the reality of 2026. We are integrating AI-driven predictive maintenance and "smart" edge controllers into our grids and pipelines. The wall between "the carpeted space" (IT) and "the hard-hat space" (OT) is now made of glass.
If a billing system failure can cause a national security crisis, then that billing system is critical infrastructure. It should be treated with the same "secure-by-design" paranoia we apply to a PLC or a turbine.
Cloaking the Crown Jewels
The irony is that IT security could learn a lot from the "minimalist" mindset of the OT world.
In OT, we want things to be silent, deterministic, and invisible. In IT, we build "God Boxes", massive, bloated operating systems that shout their presence to the entire internet. Why? Because it's "easier" for the admins.
If Colonial had Network Cloaking in 2021 (if that billing system had been invisible to the public internet, requiring a cryptographic "knock" just to see the port), those hackers would have been punching at smoke.
The Cam Cullen "Reality Check"
We need to stop pretending that "segmentation" means a firewall rule that some intern will delete next quarter. True segmentation means:
- Structural Invisibility: If the billing system is the "crown jewel," it should not be discoverable by an AI-powered scanner like Mythos.
- Minimalist Architecture: Turning off every service that isn't the core function. No SSH, no web servers, no "extra" code paths for hackers to dance on.
- Physical Guardrails: Ensuring that no IT failure - EVER - can force an OT shutdown.
As gas prices continue to climb, let’s use this anniversary for more than just a history lesson. Let's realize that in the era of AI-powered sabotage, "good enough" security is just a slow-motion disaster.
It’s time to take the crown jewels off the map. Before the pumps go dry again.
– Cam Cullen, CMO, BlastWave
The Colonial Pipeline hack exposed how one stolen VPN credential can disrupt critical infrastructure. BlastWave’s cloaking and Zero Trust approach would have stopped it before it began.
Explore the complete analysis of 23 OT attacks that defeated firewalls, VPNs, and air gaps.








.svg)